Got this this morning…

Literally 5 minutes after my director and I talked about plans to migrate to cloud…
I’ll keep my on-prem… they’ll have to pry it out of my cold dead hands before I go to the cloud with ERP.
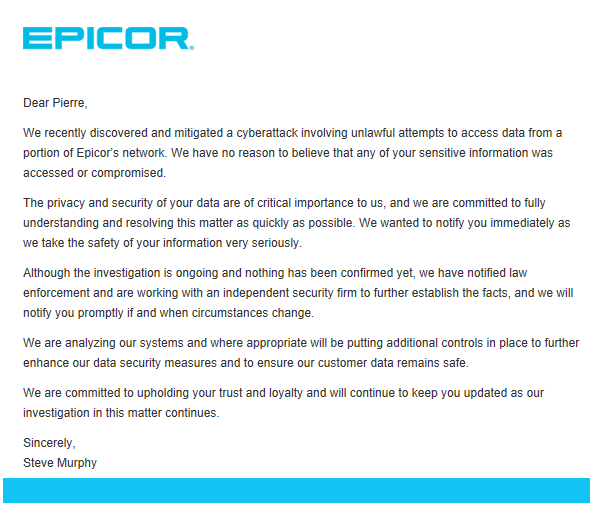
We recently discovered and mitigated a cyberattack involving unlawful attempts to access data from a portion of Epicor’s network. We have no reason to believe that any of your sensitive information was accessed or compromised.
Everyone is assuming this is an Azure breech. I’m sure they have on-prem servers too… ![]()
I wonder who believes they do security better on-prem than Microsoft does? If so, how many people would it take to replicate?
I’m not saying that Microsoft doesn’t know how to do security. Or that we are any better. But I can control the security when we host ERP on-prem. I don’t have to trust that Epicor has configured Azure right. If I misconfigure something it’s my own fault.
For Epicor to send that out, it must have been a serious breach. The only thing I can think of is someone who worked there eons ago, leaked credentials to service accounts, api keys what-not, or themselves got hit by some trojan and in return that data was stolen.
I doubt its a simple leak like viewing the users list on the Sharepoint default page.
Agreed. If it was minor and nothing was access they wouldn’t have sent it out.
Or an employee got phished and hit with Emotet and in return its disguised as cyber-breach. Just saying… Phishing emails go out daily.
Kind of odd - I didn’t receive this e-mail, and I’m the IT manager that directed our implementation…but other secondary implementation team members DID receive the e-mail.
FWIW - I got that email sent to my personal address, not the one connected to EpicCare or the Epic Portal.
And coincidentally, I signed up for those webinars yesterday, using my personal email address (so as to not connect it to my work - if they ended up charging for it)
I know there are State disclosure laws too so it may not be their decision. There’s a lot of momentum around protecting PII and financial data.
We [quote=“hasokeric, post:12, topic:73479”]
Phishing emails go out daily
[/quote]
We have to do regular online training about phishing scams. And we even have a button added to outlook to report suspected phishing scams. One of the parts of the training includes phone phishing, and gingerly dances around PC issues, by saying “Callers may have regional dialects.”
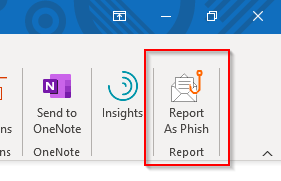
We get so many that I think some must be tests. When you report an email as Phish, a pop-up says something like “Thanks for reporting this …” (with a lot more text), but then disappears before I can finish reading it.
We got the same button, it works great!
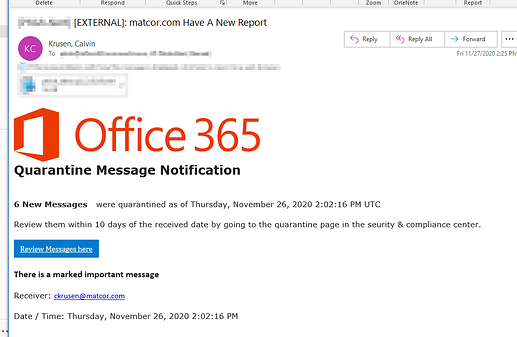
The last one I got, almost tricked me. Looked pretty authentic.
Our emails have [EXTERNAL]: prefixed to the subject, when the source is from outside our domain. But
I’ve used other corporate mail systems that use external mail filters. And the source of their messages about quarantined (possible spam) is from outside our domain. I think the above phishing attack might be more successful had it said that mail messages were being held up as possible spam. The word “quarantine” got my spidey-senses tingling.
I know of a company where email credentials were stolen (maybe from an email like the above) so when they sent items (and then removed them from the sent folder) the “External” message wasn’t there.
The lesson: always think about what you’re being asked to do no matter what the email looks like. 
This is where mouse users rule! I can hover over a link to see where its really going. Not so easy with a touch screen.
P.S. - I’ll give touchpad users some cred, as they can do the same thing. Even though mice are superior to touchpads in every way 
I wouldn’t be too confident. There are a couple of gotchas.
- It doesn’t protect one from URL shorteners
- Devs can implement their own link preview like Twitter and Facebook do
javascript - Create link previews on the client side, like in Facebook/LinkedIn - Stack Overflow